We Help With IT and Staffing Solutions
To Provide You Rapid Access To The Right Talent and Technology
Consulting, Staffing, and Software
DVO Consulting is a privately-held, female owned national IT and business consulting firm. Founded and headquartered in Salt Lake City, UT to service the ever growing silicon slopes market and the west coast. We also have offices in Great Falls, VA which supports clients in Washington DC and the east coast.
DVO Consulting provides data science services including analytics, big data, machine learning, and (AI) artificial intelligence; cybersecurity; custom software development; blockchain development; DevOps and continuous integration/delivery; as well as IT staffing and staff augmentation services.
DVO Consulting partners with public and private sector clients to solve their most difficult technology and workforce challenges through a combination of consulting, analytics, mission operations, technology platforms, systems delivery, engineering and innovation expertise.

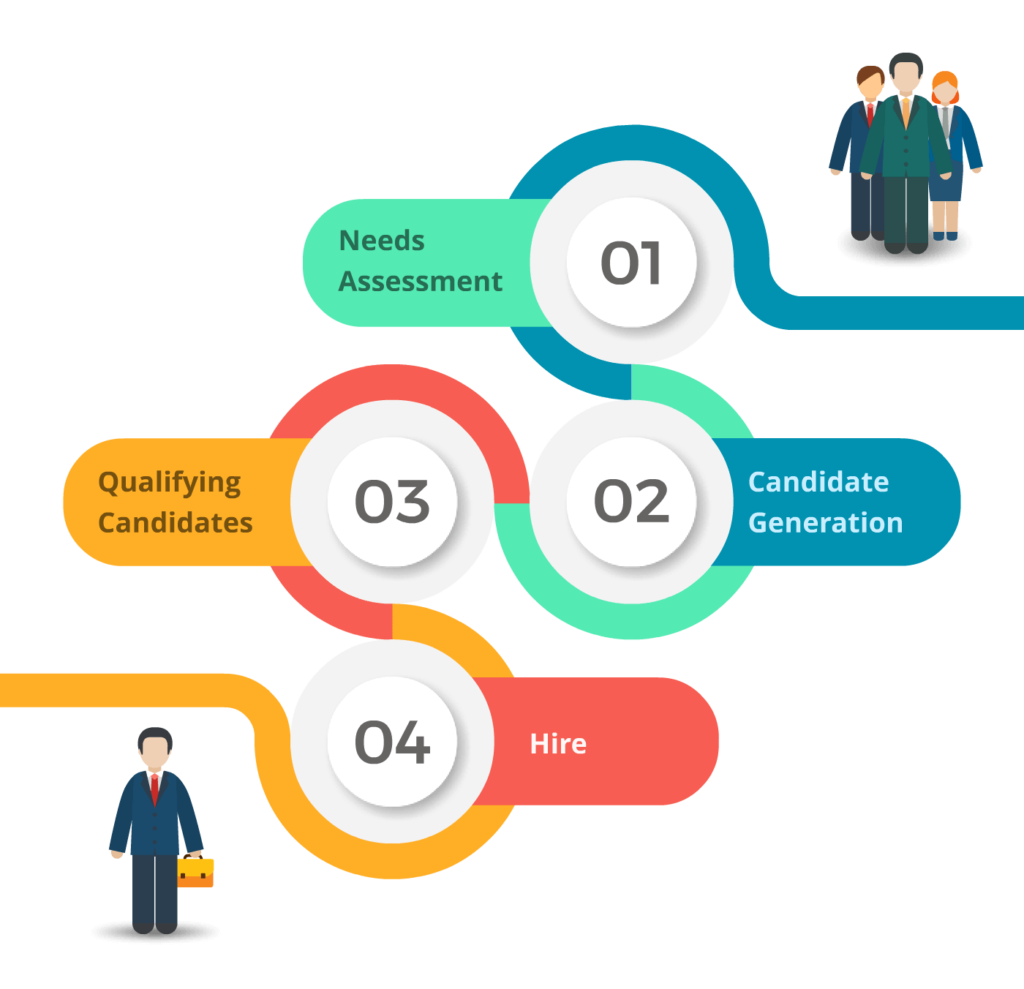
Contract to Hire and Direct Hire
Contract to hire is a situation in which an employee is hired as a contract employee for a set amount of time. At the end of that time, depending on performance, the employee would be hired as a company employee. This helps companies to try before they buy. At DVO Consulting, we can also craft a direct hire strategy to aid in the long-term success of your business.
Our direct hire services helps businesses hire full time employees of all levels within Information Technology, which supports software development, Healthcare systems, Automotive, Aerospace, Engineering, Manufacturing, Telecom, Retail, Banking & Financial Services for federal and commercial clients.
Staff Augmentation
Staff Augmentation is an outsourcing strategy which is used to staff a project and respond to business objectives in a more timely and cost efficient manner. We provide companies a competitive edge by providing experienced IT professionals with the industry’s most sought-after technical skills in key areas.
Staff augmentation includes providing Secret Clearance for information technology professionals, Cyber Security Consultants, Forensic Investigation Consultants, Data Analysts, Software Engineers, Software Architects, Web Developers and IT Project Managers.

Artificial Intelligence and Machine Learning
DVO Consulting is able to create cutting edge solutions that leverage machine learning and artificial intelligence to rapidly deliver insights and advantages from your data. We are able to create predictive models, recommender systems, scrapers, sentiment engines, and other tools which leverage both classical machine learning techniques and deep learning.
Our team of data scientists and engineers will work with your organization to locate relevant sources of information that will help you meet your project goals. From there, we will partner with organization leadership to build a complete project assessment and development plan and work towards the implementation of a prototype. DVO consulting is also able top provide hosting and management for the solution in order to maximize uptime and performance.

Big Data Services

Blockchain Services
DevOps Engineering

Call Us Today To Talk About Your Project
View Our Software and Staffing Articles
